E-Sign for Financial Services Compliance: An Expert Guide
Master e-sign for financial services compliance. Our guide covers ESIGN, audit trails, and technical controls to ensure your e-signatures are legally binding.
Tired of nonsense pricing of DocuSign?
Start taking digital signatures with BoloSign and save money.
A lot of financial services teams are in the same bind right now. The business wants account opening, loan packets, advisory agreements, disclosures, and internal approvals to move faster. Compliance wants proof that every signature is valid, every consent is documented, and every record can stand up in an audit or a dispute.
That tension is where most e-sign projects succeed or fail.
The mistake I see most often is treating e-signature rollout as a document workflow upgrade instead of a compliance system. In finance, the signature is only one piece. The essential work sits underneath it: consumer consent, authentication, audit evidence, access control, retention, and a process your operations team can run every day without improvising.
The High Stakes of Digital Signatures in Finance
A regional lender launches digital closing before quarter-end. Approval times drop immediately. Two months later, compliance pulls a sample file and finds the harder problem: the signed PDF is there, but the institution cannot show, with clean evidence, which disclosures the borrower saw, how consent to receive records electronically was captured, or whether the final document was the same version presented for signature.
That is the primary risk in finance. A fast signing experience can still leave an institution exposed during an exam, a customer dispute, or litigation.

Digital signatures affect more than document turnaround. They affect evidentiary strength, operational control, and the institution’s broader approach to regulatory compliance for banks. IT, compliance, legal, and operations all depend on the same answer: can the organization prove what happened in a way a regulator, auditor, or judge will accept?
A common mistake is treating e-signature rollout as a front-end workflow project. In practice, it is a control framework. The signature event matters, but the defensibility sits underneath it: verified identity, affirmative consent, document integrity, timestamping, access controls, retention, and audit evidence that can be exported without manual reconstruction.
The pressure shows up first in a few predictable workflows, and each one fails in a different way if the design is weak:
- Consumer lending: Problems usually start with consent capture, disclosure presentation, and missing evidence that the borrower could access records electronically.
- Retail banking: Account opening flows often inherit branch-era assumptions, then break in digital channels where identity proofing and acceptance steps need to stand on their own.
- Wealth and advisory: Higher-value relationships create higher evidentiary expectations. Firms need clear proof around who signed, what version was signed, and how records were retained.
- Internal compliance operations: Policy attestations, approvals, and exception sign-offs also need traceability. Internal documents are often challenged during investigations because teams assume lower risk and collect weaker evidence.
Here is the practical test I use. If your team cannot explain how a record was presented, how the signer authenticated, how consent was captured, how the final version was sealed, and how the audit log was preserved, the process is incomplete.
Well-designed e-signature programs reduce friction and strengthen control at the same time. Poorly designed ones only move the point of failure from paper handling to evidence handling.
Understanding the Legal Framework for E-Signatures
A loan package can clear every internal approval, reach the customer on time, and still create litigation risk if the institution cannot prove how the customer consented to receive records electronically. That is the point many teams miss. In financial services, the legal framework is not just a permission slip for e-signatures. It is a set of evidence requirements that your workflow has to satisfy under scrutiny.
The US baseline starts with the Electronic Signatures in Global and National Commerce Act, effective in 2000, and with UETA at the state level. Together, they recognize electronic signatures and records for most transactions, provided the process can show intent, consent where required, record association, and accurate retention.

The hard part is not legal theory. The hard part is proving, after the fact, that your implementation met those conditions for a specific transaction.
What ESIGN and UETA mean in practice
For an IT director, four legal requirements translate into four design questions.
Intent to sign
The signer has to take a clear action that shows intent. A typed name, a click to sign, or a certificate-based signature can all work if the action is deliberate and captured in the event log. Passive conduct is weak evidence.Consent to do business electronically
Many consumer-facing implementations fail on this front. If paper disclosures are being replaced with electronic delivery, the institution needs proof that the consumer agreed to that method and, in many cases, could access the records in the format provided. A pre-checked box and a generic platform timestamp are often not enough in a contested matter.Association of the signature with the record
You need evidence that the signer accepted the exact version presented at signing. That requires controlled templates, immutable document hashes, and disciplined document version control in e-signature workflows. If operations can swap files after review but before execution, the legal argument gets weaker fast.Retention and accurate reproduction
The institution must be able to reproduce the record later in a form that remains accurate and accessible. That affects storage architecture, export formats, encryption key management, and retention policy, not just the signing screen.
UETA generally mirrors these principles at the state level, which is why most financial institutions treat ESIGN and UETA as one operating standard. That is the practical approach. Build one evidence model that works for both, then document any state-specific exceptions your products trigger.
For teams working through broader bank obligations, regulatory compliance for banks is a useful reference because it places e-signature controls inside the wider governance, reporting, and risk framework banks already manage.
Why eIDAS matters even for US-led firms
A firm may consider itself US-only until a guarantor is in Germany, an investor entity is in Luxembourg, or a treasury agreement involves an EU counterparty. At that point, eIDAS stops being a foreign legal acronym and starts affecting vendor selection, assurance levels, and admissibility planning.
The practical issue is not whether every agreement needs the highest signature tier. Most do not. The issue is whether your platform can support different assurance levels without forcing a separate process for each geography.
| Framework | What matters operationally |
|---|---|
| ESIGN | Federal recognition of electronic signatures and records in US commerce |
| UETA | State-level legal framework for electronic transactions |
| eIDAS | EU trust framework with defined signature levels and stronger expectations around identity assurance for some use cases |
In implementation terms, that means mapping transaction risk to authentication strength, evidence capture, and certificate method. A low-risk internal acknowledgment should not carry the same friction as a cross-border funding agreement. But both should be defensible.
The strongest programs answer a regulator’s real question: can the institution prove this signer, this document, this consent event, and this record history for this exact transaction. That standard is what separates a legally aware e-signature rollout from one that only appears compliant on paper.
Building an Ironclad Audit Trail for Every Transaction
The signature image on a PDF is not the legal evidence. The evidence is the chain of events around it.

A compliant platform should generate a Certificate of Evidence for each document. That record captures signer IP addresses, precise timestamps, and authentication methods, and it is cryptographically bound to the document using standards such as X.509 PKI so the document can’t be altered after execution, as explained in BlueInk’s financial-services e-signature guide.
What a defensible audit trail needs to show
If your compliance team ever has to answer a regulator, internal auditor, examiner, or outside counsel, the audit trail should let them reconstruct the transaction without guesswork.
At minimum, look for these elements:
- Document identity: The exact file or template version presented to the signer.
- Signer trail: Who received it, who opened it, and who completed each required action.
- Time sequence: Event timestamps that show the order of presentation, consent, authentication, and signature.
- Authentication record: Whether the signer used email verification, SMS OTP, MFA, or another method.
- Tamper evidence: Proof that the record was sealed after signing and hasn’t changed.
- Storage and retrieval path: A reliable way to retrieve the signed file and supporting evidence later.
That’s also why document versioning matters before a file is sent. If an operations team updates a disclosure or agreement template and no one can prove which version was sent, the record gets weaker immediately. Disciplined version control then becomes integral to compliance, rather than solely document management. BoloSign’s guide to document version control is useful because it explains how version drift creates avoidable evidence problems.
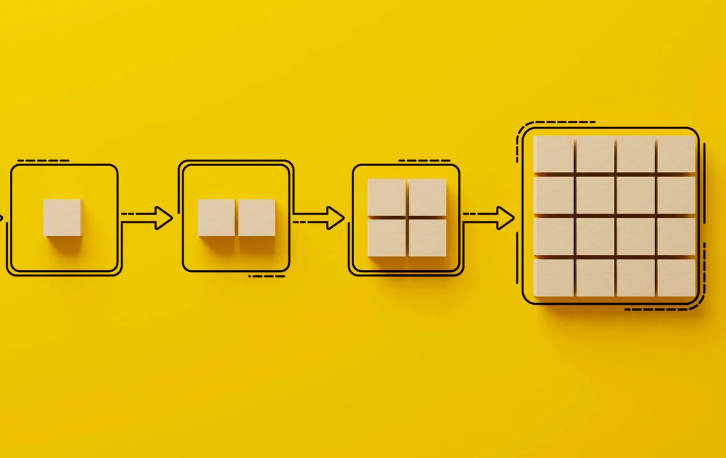
Authentication should match transaction risk
Not every financial workflow needs the same identity assurance.
A low-risk internal approval may be fine with a standard recipient flow. A consumer lending package, wire-related authorization, mortgage disclosure, or high-value advisory document usually needs stronger authentication and cleaner chain-of-custody evidence.
A practical risk model often looks like this:
| Use case | Typical control posture |
|---|---|
| Internal policy acknowledgment | Basic user authentication and full audit logging |
| Customer onboarding | Explicit consent, signer verification, audit record, secure retention |
| Loan or mortgage documentation | Stronger authentication, detailed evidence certificate, tamper sealing |
| Cross-border financial agreement | Jurisdiction-aware workflow, stronger identity controls, retention mapping |
Here’s a useful visual summary of how that sequence should work in production.
What fails in real environments
The weak points are rarely exotic. They’re procedural.
- Teams email unsigned PDFs outside the platform and lose central evidence.
- Admins overwrite templates without controlling published versions.
- Authentication is too weak for the transaction type because one default workflow is used for everything.
- Signed files are stored separately from audit artifacts so retrieval becomes manual and unreliable.
- Operations staff fix edge cases offline and create undocumented exceptions.
Keep the evidence package attached to the document lifecycle itself. If your team has to assemble proof from email threads, CRM notes, and shared drives after the fact, the process is already fragile.
An ironclad audit trail isn’t about collecting more data. It’s about collecting the right evidence in the right sequence and preserving it without manual patchwork.
Mapping Technical Controls to Regulatory Requirements
Compliance teams often describe obligations in legal language. IT teams buy and configure software based on features. Problems start when those two lists never get translated into each other.

A more useful evaluation method is to map each compliance requirement to a control you can configure, monitor, and audit.
A working control map
Here’s the kind of mapping I use when reviewing an e-sign platform for a bank, lender, or fintech team:
| Requirement | Technical control |
|---|---|
| Intent and signer attribution | Named recipient routing, authenticated access, event logging |
| Record integrity | Tamper-evident sealing, cryptographic binding, version control |
| Consumer consent | Separate consent step, capture logs, reproducible records |
| Retention | Secure cloud storage, retrieval controls, retention policy support |
| Restricted access | Role-based access controls, least-privilege permissions, SSO |
| Vendor assurance | Independent certifications and documented security controls |
For readers who want a broader legal framing, this explanation of regulatory compliance is a helpful refresher on how organizations convert legal duties into repeatable operational controls.
What to verify in the platform before procurement
Don’t stop at the feature checklist on a pricing page. Ask how the control works.
Focus on these questions:
- Encryption: How are documents protected in transit and at rest?
- Access management: Can you enforce role-based permissions by team, document type, or workflow stage?
- Identity architecture: Does the platform support stronger authentication where required?
- Retention discipline: Can records and audit evidence be retained together and retrieved cleanly?
- Admin governance: Are template changes, policy updates, and user provisioning controlled centrally?
- Third-party assurance: Does the vendor provide recognized security certifications and clear documentation?
Identity and lifecycle controls matter even more in enterprise environments where staff changes, delegated administration, and multiple business units create risk. If your firm uses centralized identity tooling, this review of enterprise-grade e-sign tools with SSO and SCIM is worth reading because user provisioning and deprovisioning are often overlooked in signature projects.
What usually doesn’t work
A platform may look compliant in a demo and still fail operationally if it depends on too many manual decisions.
Common examples include:
- a shared admin login for multiple teams
- unrestricted template editing
- unsigned side agreements sent through email
- no separation between test and production workflows
- no retention ownership between compliance, IT, and records teams
The best technical control set is the one your staff can execute consistently under normal workload. Fancy features don’t help if exceptions force people outside the system.
Implementing a Compliant E-Signature Workflow
A borrower is ready to close, operations has the documents queued, and the business wants the packet out before end of day. If the workflow asks for a signature before valid consumer consent is captured and proved, speed becomes a legal risk. In financial services, that is the point where a fast digital process can fail in an audit or become harder to defend in a dispute.
Implementation starts with workflow design. The legal standard matters, but the operational question is more specific: can your team show, record by record, that the right person received the right disclosures, consented to electronic delivery in a valid way, and signed through a controlled process that preserved the evidence?
The consent step is where many deployments break down. ESIGN is not satisfied by a generic checkbox dropped into the signing screen. For consumer transactions, the process has to capture affirmative consent and support the firm’s ability to show the consumer could access the electronic records in the format used. If that proof is weak, the signature event itself may be less useful than teams expect.
Build the workflow in this order
A defensible rollout usually follows this sequence:
Classify the transaction Separate internal approvals from customer-facing financial agreements. Then split consumer transactions from commercial ones. A treasury management form, a retail lending disclosure, and an internal policy acknowledgment should not ride the same workflow.
Design the consent event Present the electronic records disclosure before the signing step, not inside it as an afterthought. Include delivery terms, withdrawal rights, hardware and software requirements, and a method to demonstrate access to the record format you will use.
Apply the right authentication Match identity controls to risk. A low-risk internal acknowledgment may justify basic email access. A loan modification, account opening packet, or other regulated customer agreement may need stronger authentication, step-up verification, or additional knowledge of the signer’s identity drawn from your existing systems.
Control the document package Lock templates, field placement, signer order, and conditional clauses before operations starts sending live documents. Freeform editing by front-line staff creates evidence gaps and inconsistent disclosures.
Store one evidence file Retain the signed document, consent record, delivery logs, authentication events, timestamps, hash or tamper-evidence data, and completion certificate together. If these records live in separate systems without a stable transaction ID, retrieval becomes expensive and error-prone.
The point that deserves more engineering time
The access demonstration requirement is usually treated as legal wording. It is really a systems design issue.
Compliance and IT should decide early how the user will prove access, what file type will be used for disclosures, how exceptions are handled, and when consent must be refreshed after a material change. Email changes, mobile-only usage, delegated inboxes, and broken attachment rendering all affect whether your evidence will hold up later. If your answer is "the platform logs that the email was sent," the design is not finished.
I usually recommend mapping this flow at the event level. What was shown to the consumer, in what format, on what device or browser context, what action demonstrated access, what version of the disclosure was in force, and where that evidence is stored. That is the level of detail regulators and litigators care about once a transaction is challenged.
If consent is captured as a simple checkbox without supporting event data, the process may be digital but it is not very defensible.
What the workflow looks like in practice
Take a consumer loan application. The borrower receives a controlled invitation, reviews the electronic records disclosure, completes the consent step, and only then enters the signing flow. The system logs the consent event, ties it to the disclosure version, records the authentication events, presents the documents in order, captures the signature, seals the completed record, and pushes the full evidence package into the LOS or archive under the same transaction reference.
That structure works because it reduces human judgment during execution. Operations is not deciding, case by case, whether consent language was included or whether the final PDF was saved in the right folder. The workflow makes those decisions in advance.
Platform selection affects how easy this is to maintain. For teams comparing e-sign platforms for enterprise workflows, the useful questions are operational: can the system enforce template controls, preserve consent and signature evidence together, support integration into systems of record, and apply different verification steps by transaction type? Platforms like BoloSign are designed to support these compliance-focused workflows with standardized templates and integrated audit trails.
What works and what fails under pressure
What works:
- transaction-specific workflows instead of one generic signing path
- consent capture that is separate, versioned, and retained with the final record
- authentication rules tied to document risk
- locked templates with controlled change management
- integrations that move the evidence package without breaking traceability
- named ownership across compliance, IT, operations, and records management
What fails under pressure:
- manual exception handling outside the platform
- copied consent language with no proof model behind it
- storing only the executed PDF
- allowing staff to edit regulated templates ad hoc
- measuring rollout success only by send speed or completion rate
A compliant workflow should feel routine to the operations team. That usually means the design work was done properly upstream, where legal requirements, evidence capture, and system controls were translated into steps staff can execute the same way every time.
Navigating Cross-Border and Global Compliance
Financial services agreements don’t stay neatly inside one jurisdiction for long. A Canadian client signs with a US affiliate. An Australian entity is part of a lending group. A UAE counterparty needs a contract executed from a platform managed elsewhere.
The core principles stay familiar. You still need intent, reliable attribution, record integrity, retention, and the right consent model. What changes is the assurance level and legal framing expected in each market.
A practical way to think about jurisdiction fit
For firms operating across the US, Canada, Australia, New Zealand, and the UAE, I recommend a simple rule set:
- Use one governed workflow framework across regions so operations teams aren’t improvising by country.
- Adjust authentication and evidence depth by transaction type and jurisdiction.
- Confirm which transactions need local legal review before assuming a standard electronic signature flow is enough.
- Keep records in a format that can be reproduced cleanly for review, dispute resolution, or cross-border compliance checks.
eIDAS matters here because it pushed the market toward stronger trust standards for cross-border execution. Even if your primary volume is outside Europe, the discipline it introduced is useful when evaluating enterprise platforms.
For teams comparing platform design for multinational operations, this review of e-sign platforms for enterprise workflows gives a practical lens for assessing governance, scalability, and fit across distributed teams.
The wrong global strategy is maintaining separate signing habits by office. The right one is using a common operating model and escalating controls where the jurisdiction or transaction requires it.
Your Actionable E-Signature Compliance Checklist
If you’re evaluating a vendor or auditing an existing process, use this list to pressure-test the rollout.
Legal and process checks
- Validate transaction scope: Confirm which financial workflows can be handled electronically and which require additional review.
- Review consent requirements: Make sure consumer-facing electronic records use affirmative consent where required.
- Test access demonstration: Verify the process shows the consumer can access the records electronically.
- Document withdrawal handling: Confirm the workflow explains how consent can be withdrawn or delivery details updated.
Evidence and audit checks
- Require a complete audit record: Every signed document should have a retrievable evidence package.
- Preserve document integrity: Signed records should be sealed against post-execution change.
- Tie signature to version: The system must show exactly which document or template version was signed.
- Keep records together: Don’t split the final document from its supporting audit artifacts.
Security and administration checks
- Enforce role-based access: Limit who can send, edit, approve, view, and export sensitive documents.
- Control identity lifecycle: Make provisioning and deprovisioning part of the implementation, not an afterthought.
- Review retention controls: Confirm signed records can be stored and retrieved according to policy.
- Examine vendor security posture: Ask for certification details, security documentation, and admin-control visibility.
Operational checks
- Standardize templates: Don’t let each department build ad hoc signing packets.
- Design exception handling: Decide in advance how out-of-policy or cross-border edge cases are managed.
- Integrate with systems of record: CRM, LOS, document repositories, and compliance systems should support the workflow instead of fragmenting it.
- Train for consistency: The best compliance design still fails if frontline teams work around it.
A solid e-sign for financial services compliance program should reduce friction for staff and increase confidence for compliance, legal, and audit teams at the same time.
If you want to test a practical way to create, send, and sign PDFs, templates, and forms with AI-powered contract automation, compliance support, and predictable pricing, try BoloSign. It’s built for teams that need secure digital signing solutions without complicated rollout overhead, and you can start with a 7-day free trial to see how it fits your workflow.

Paresh Deshmukh
Co-Founder, BoloForms
21 Apr, 2026
Take a Look at Our Featured Articles
These articles will guide you on how to simplify office work, boost your efficiency, and concentrate on expanding your business.